Challenges in Cybersecurity
Primarily intended as civilian space – now officially declared a been officially declared as the 5th dimension of warfare after land, sea, air and space.
- Absence of any geographical barriers
- difficult attribution as attacker is difficult to locate
- cyberspace technology is rapidly evolving
- foolproof cybersecurity architecture is nearly impossible
Cyber Crimes in India
- a surge of about 350 % in cybercrime cases registered from 2011 to 2014 – a study by ASSOCHAM.
- cyber-attacks on government sector doubled from 14% in 2016 from 7% in 2015
- Wannacry Ransomware – infected more than 1 Lakh computers all over the world
- Hacker group “Legion” broke into Twitter accounts of the Congress Party, its vice president & Vijay Mallya
Critical Information Infrastructure
- refers to ICT systems that are essential for the operations of national & international crucial Infrastructures like telecommunication networks, online payment gateways, electronic stock trading.
- incapacitation or destruction of which have debilitating impact on national security & economy – Since the price of their failure is too high, they are prone to attacks from state and non- state actors
Factors Responsible
- Adversary nations: cyber-attacks by Russia on Georgia, use of Stuxnet malware to damage Iran’s nuclear facility
- Latest technologies & electronic components are procured via global supply chain – Can be tampered & inserted with malicious software
- Inside threat by disgruntled/compromised employee – hacking and subsequent revelations by Edward Snowden caused a global havoc
- If an employee is inadequately trained, chances of CII disruption or damage by accident are higher.
- technology permits attacker to conceal its origin making it more lucrative for the state and non-state actors
- No conventional restrictions of being in proximity to start an attack – Can be done from any location to affect systems anywhere in the world
Financial Sector
- Attacks on the financial sector rose from 3% in 2015 to 14% in 2016
- 19 Indian Banks faced a series of data theft in last 6 months – biggest debit card fraud in Indian history – Banks have recalled and blocked more than 32 lakh debit cards – NPCI on probing found a malware-induced security breach in systems of Hitachi Payment Services, which provides ATMs, point of sale & other services in India.
Government plan of Digital India to bring about socio-economic changes via –
- increasing financial inclusion + better targeting of subsidies
- improving economic efficiency by lowering transaction costs
- moving toward a cashless economy to reduce the circulation of black money & curb tax evasion
Demonetisation & shift to a cashless economy. This has to be seen in the light of the leak of information related to 32 million debit cards recently. The fraud, thus, exposes the vulnerability of Indian financial structure. If not tackled immediately with effective means this could be a huge setback for the government.
[clear]Issues in India’s Cybersecurity
- Computer Emergency Response Team (CERT-In) is woefully understaffed.
- The private sector is culpable in its failure to report and respond to breaches in digital networks. Interpol data says that less than 10 % of such cases were registered with law enforcement agencies.
- Although Gov. has set up National Critical Information Infrastructure Protection Centre (NCIIPC) but it is yet to identify and implement measures to protect critical information infrastructure
- Attitudinal factor – The continued perception has been that cyber security is “optional”
- International threat of a cyber-war from countries like China and Pakistan
- Lots of equipment’s in India are imported. It is unknown whether these devices are tampered with or programmed for control processes
Steps Taken By Government
- Sectoral CERTs have been functioning in the areas of Defence & Finance for catering to critical domains
- Creation of NCIIPC – envisaged to act as a 24×7 centre to battle cyber security threats in strategic areas such as air control, nuclear and space.
- I4C (Indian Cyber Crime Coordination Center) has been set up in 2016 to look into every kind of cybercrime.
- National Cyber Coordination Centre to handle online threats relating to national security
- Information Security Education & Awareness project to develop human resource in this field
- teamed up with countries like USA, UK and China for mutual sharing of information and bestpractices.
- Cyber Swachhta Kendra– Botnet Cleaning and Malware Analysis Centre for analysis of malware and botnets that affect networks and systems
For Financial Sector
- Budget proposed of Computer Emergency Response Team for the Financial Sector (CERT-Fin)
- RBI directed banks to implement a security policy containing strategy for dealing with cyber threats
- RBI had already created a specialised cell to conduct detailed IT examination of banks’ cyber security preparedness
- Maharashtra has become 1st state in the country to have a cyber-police station in each district simultaneously.
Need of CERT-Fin
- exponential growth in digital payments and the push towards a cashless economy
- Banks and financial institutions are vulnerable to various forms of cyber-attacks and online frauds
- ATM and retail banking are also increasingly vulnerable to cybercrime
- Mobile frauds are also expected to grow to 60-65% in 2017
Indian Computer Emergency Response Team (CERT-in)
Main Function – working 24/7 & scanning the cyber space in the country to provide early security warning and effective incident response. It has been designated to serve as the national agency to perform the following functions:
- Forecast and alerts of cyber security incidents
- Emergency measures for handling cyber security incidents
- Coordination of cyber incident response activities
- Issue guidelines, advisories, and whitepapers relating to information security practices, procedures, prevention, response and reporting of cyber incidents
Information Technology (IT) Act 2000
- a legal framework for transactions carried out by means of electronic data interchange
- amended through Information Technology (Amendment) Act, 2008 – Added provisions like to deal with new forms of cyber-crimes like publicizing sexually explicit material in electronic form, video voyeurism, cyber terrorism, breach of confidentiality and leakage of data by intermediary and ecommerce frauds.
National Cyber Security Policy 2013
- Set up different bodies to tackle various levels of threats, along with CERT, to coordinate all matters related to cyber security.
- Create NCIIPC
- Create a workforce of around 5 Lakh trained in cyber security.
- Provide fiscal benefits to businesses to adopt best security practices.
- Set up testing labs to regularly check the safety of equipment being used in the country.
- Create a cyber-ecosystem in the country, developing effective public-private partnerships
- Building indigenous security technologies through research.
Way Forward
- consider acceding to Budapest convention.
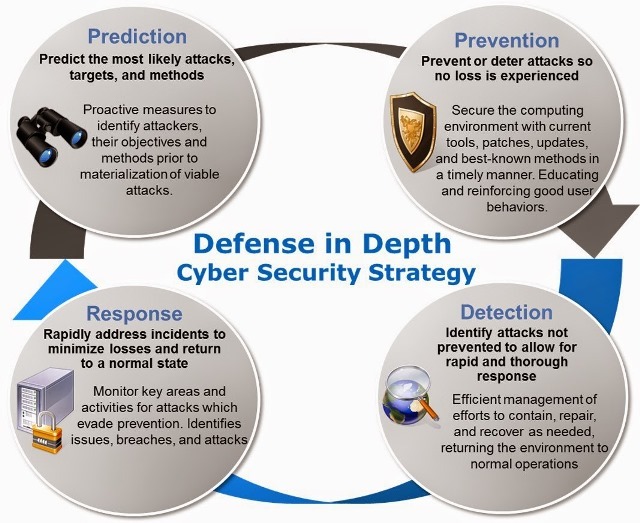
- Cyber Security mock drills to prepare the organizations to detect, mitigate and prevent cyber incidence
- The idea of a National Cyber Registry “as a repository of IT professionals” should be implemented.
- Concept of air gapping which isolate the critical infrastructures from the internet should be used.
- India must push for an international court to prosecute transnational cyber crime
- need to develop the offensive capabilities as well rather than being merely defensive.
- Create a cyber-ecosystem in the country, developing effective public-private partnerships
Budapest Convention – only multilateral treaty on cyber security that addresses Internet and computer crime – Developing countries including India have not signed it stating that the developed countries lead by the US drafted it without consulting them